Computer/network security hinges on two very simple goals: Show
There are a number of components involved in accomplishing these objectives. One way is to assign access permissions to resources that specify which users can or cannot access those resources and under what circumstances. (For example, you may want a specific user or group of users to have access when logged on from a computer that is physically on-site but not from a remote dial-up connection.) Access permissions, however, work only if you are able to verify the identity of the user who is attempting to access the resources. That’s where authentication comes in. In this Daily Drill Down, we will look at the role played by authentication in a network security plan, popular types of authentication, how authentication works, and the most commonly used authentication methods and protocols. Authentication and security Authentication vs. authorization For example, when a user who belongs to a Windows domain logs onto the network, his or her identity is verified via one of several authentication types. Then the user is issued an access token, which contains information about the security groups to which the user belongs. When the user tries to access a network resource (open a file, print to a printer, etc.), the access control list (ACL) associated with that resource is checked against the access token. If the ACL shows that members of the Managers group have permission to access the resource, and the user’s access token shows that he or she is a member of the Managers group, that user will be granted access (unless the user’s account, or a group to which the user belongs, has been explicitly denied access to the resource). Another example of authorization is the Dialed Number Identification Service (DNIS), which authorizes a dial-in connection based on the number called. Logon authentication Network access authentication IPSec authentication An important consideration is that both the sending and receiving computers must be configured to use a common authentication method or they will not be able to engage in secured communications. IPSec configuration If IPSec policies have been configured to require that communications be secured, the sending and receiving computers will not be able to communicate at all if they do not support a common authentication method. Remote authentication There are a number of authentication methods that can be used to confirm the identity of users who connect to the network via a remote connection such as dial-up or VPN. These include:
Remote users can be authenticated via a Remote Authentication Dial-In User Service (RADIUS) or the Internet Authentication Service (IAS). Each of these will be discussed in more detail in the section titled Authentication Methods and Protocols. It is especially important that remote users be properly authenticated, as they generally pose a greater security risk than on-site users. Single Sign-On
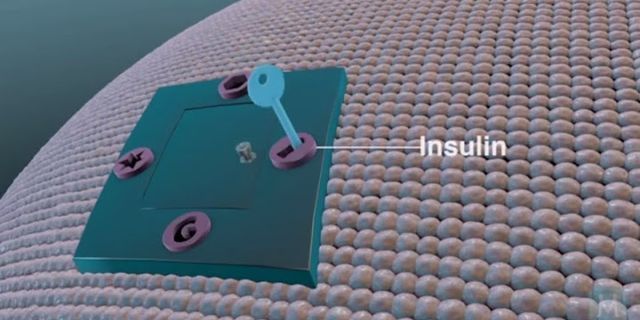
(SSO) There are a number of SSO products on the market that allow for single sign-on in a mixed (hybrid) environment that incorporates, for example, Microsoft Windows servers, Novell NetWare, and UNIX. Details on SSO For a more detailed discussion of SSO, see Single Sign-On Solutions in a Mixed Computing Environment. Authentication types There are several physical means by which you can provide your authentication credentials to the system. The most common—but not the most secure—is password authentication. Today’s competitive business environment demands options that offer more protection when network resources include highly sensitive data. Smart cards and biometric authentication types provide this extra protection. Password authentication To preserve the security of the network, passwords must be “strong,” that is, they should contain a combination of alpha and numeric characters and symbols, they should not be words that are found in a dictionary, and they should be relatively long (eight characters or more). In short, they should not be easily guessed. Password authentication is vulnerable to a password “cracker” who uses a brute force attack (trying every possible combination until hitting upon the right one) or who uses a protocol “sniffer” to capture packets if passwords are not encrypted when they are sent over the network. Smart card authentication Smart cards use cryptography-based authentication and provide stronger security than a password because in order to gain access, the user must be in physical possession of the card and must know the PIN. For more detailed information about how smart cards work, see my TechProGuild Daily Drill Down “Enhancing security with the use of smart cards.” Biometric authentication In addition to fingerprints, voice, retinal, and iris patterns are virtually unique to each individual and can be used for authentication purposes. This method of proving one’s identity is very difficult to falsify, although it requires expensive equipment to input the fingerprint, voice sample, or eye scan. Another advantage over smart cards is that the user does not have to remember to carry a device; his or her biological credentials are never left at home. Biometrics For more information about biometrics, see this article at Network Computing. How does authentication work? In theory, authentication is relatively simple: A user provides some sort of credentials—a password, smart card, fingerprint, digital certificate—which identifies that user as the person who is authorized to access the system. There are, however, a multiplicity of methods and protocols that can be used to accomplish this. Regardless of the method, the basic authentication process remains the same. The authentication process When the user wants to log on, he or she provides the credentials and the system checks the database for the original entry and makes the comparison. If the credentials provided by the user match those in the database, access is granted. Advantages of multilayered authentication Authentication methods and protocols
These are by no means the only authentication methods in existence, but they are some of the most common. Kerberos A Key Distribution Center (KDC) is a service that runs on a network server, which issues a ticket called a Ticket Granting Ticket (TGT) to the clients that authenticates to the Ticket Granting Service (TGS). The client uses this TGT to access the TGS (which can run on the same computer as the KDC). The TGS issues a service or session ticket, which is used to access a network service or resource. The name Kerberos derives its name from the three-headed dog of Greek mythology (spelled Cerberus in Latin) that guarded the gates to Hades. Kerberos likewise stands guard over the network to ensure that only those who are authorized can enter. Secure Sockets Layer (SSL) The SSL protocol is another Internet standard, often used to provide secure access to Web sites, using a combination of public key technology and secret key technology. Secret key encryption (also called symmetric encryption) is faster, but asymmetric public key encryption provides for better authentication, so SSL is designed to benefit from the advantages of both. It is supported by Microsoft, Netscape, and other major browsers, and by most Web server software, such as IIS and Apache. SSL operates at the application layer of the DoD networking model. This means applications must be written to use it, unlike other security protocols (such as IPSec) that operate at lower layers. The Transport Layer Security (TLS) Internet standard is based on SSL. SSL authentication is based on digital certificates that allow Web servers and clients to verify each other’s identities before they establish a connection. (This is called mutual authentication.) Thus, two types of certificates are used: client certificates and server certificates. SSL overview An excellent overview of how SSL works, Introduction to SSL, can be found at Netscape. Microsoft NTLM (NT LAN Manager) NTLM authentication is used by Windows NT servers to authenticate clients to an NT domain. Windows 2000 uses Kerberos authentication by default but retains support for NTLM for authentication of pre-Windows 2000 Microsoft servers and clients on the network. UNIX machines connecting to Microsoft networks via an SMB client also use NTLM to authenticate. Native mode If you convert your Windows 2000 domain’s status to native mode, NTLM support will be disabled. NTLM uses a method called challenge/response, using the credentials that were provided when the user logged on each time that user tries to access a resource. This means the user’s credentials do not get transferred across the network when resources are accessed, which increases security. The client and server must reside in the same domain or there must be a trust relationship established between their domains in order for authentication to succeed. PAP The advantage of PAP is that it is compatible with many server types running different operating systems. PAP should be used only when necessary for compatibility purposes. SPAP The client sends the user name along with the encrypted password, and the remote server decrypts the password. If the username and password match the information in the server’s database, the remote server sends an Acknowledgment (ACK) message and allows the connection. If not, a Negative Acknowledgment (NAK) is sent, and the connection is refused. CHAP and MS-CHAP This has obvious security advantages over PAP/SPAP, as the password does not go across the network and cannot be captured. CHAP specs The specifications for CHAP are discussed in RFC 1994. The hash algorithm ensures that the operation cannot be reverse engineered to obtain the original password from the hash results. CHAP is, however, vulnerable to remote server impersonation. MS-CHAP is Microsoft’s version of CHAP. MS-CHAPv2 uses two-way authentication so that the identity of the server, as well as the client, is verified. This protects against server impersonation. MS-CHAP also increases security by using separate cryptographic keys for transmitted and received data. EAP A key characteristic of EAP is its extensibility, indicated by its name. Plug-in modules can be added at both client and server sides to support new EAP types. EAP can be used with TLS (called EAP-TLS) to provide mutual authentication via the exchange of user and machine certificates. RFC EAP-TLS is defined in RFC 2716. EAP can also be used with RADIUS (see below). RADIUS RADIUS can also perform accounting services, and EAP messages can be passed to a RADIUS server for authentication. EAP only needs to be installed on the RADIUS server; it’s not required on the client machine. Windows 2000 Server includes a RADIUS server service called Internet Authentication Services (IAS), which implements the RADIUS standards and allows the use of PAP, CHAP, or MS-CHAP, as well as EAP. Certificate services Certificates are issued by certification authorities (CAs), which are trusted entities that “vouch for” the identity of the user or computer. The CA digitally signs the certificates it issues, using its private key. The certificates are only valid for a specified time period; when a certificate expires, a new one must be issued. The issuing authority can also revoke certificates. Certificate services are part of a network’s Public Key Infrastructure (PKI). Standards for the most commonly used certificates are based on the X.509 specifications. Information on certificate services Windows 2000 includes support for certificate services. For more information, see this page on Microsoft’s support site. Conclusion Authentication is a vital part of a network’s security scheme, as it is the mechanism for ensuring that the identity of a user, computer, or service is valid. There are a number of ways that authentication can be accomplished, depending on network operating system and connection type. In this Daily Drill Down, I have provided an overview of some of the most common authentication methods, under what circumstances each is used, and how they work. What are 3 ways to authenticate a user?There are three common factors used for authentication: Something you know (such as a password) Something you have (such as a smart card) Something you are (such as a fingerprint or other biometric method)
What are the different ways of authenticating users?Here are just a few of those methods.. Single-Factor/Primary Authentication. ... . Two-Factor Authentication (2FA) ... . Single Sign-On (SSO) ... . Multi-Factor Authentication (MFA) ... . Password Authentication Protocol (PAP) ... . Challenge Handshake Authentication Protocol (CHAP) ... . Extensible Authentication Protocol (EAP). What are those 4 commonly authentication methods?The most common authentication methods are Password Authentication Protocol (PAP), Authentication Token, Symmetric-Key Authentication, and Biometric Authentication.
What are the 3 types of authentication?Authentication factors can be classified into three groups: something you know: a password or personal identification number (PIN); something you have: a token, such as bank card; something you are: biometrics, such as fingerprints and voice recognition.
|